False information about drug shortages, heating and food, domains using the name of Alexei Navalny, messages suggesting that Ukrainian citizens voluntarily amputate their limbs as a way to avoid military service, and eating pigeons as a recipe for potential product shortages – these are the messages transmitted as part of a disinformation, psychological campaign that cybercriminals associated with Russia carried out from September 2023 to January 2024. These shocking actions were unmasked by ESET cybersecurity experts.
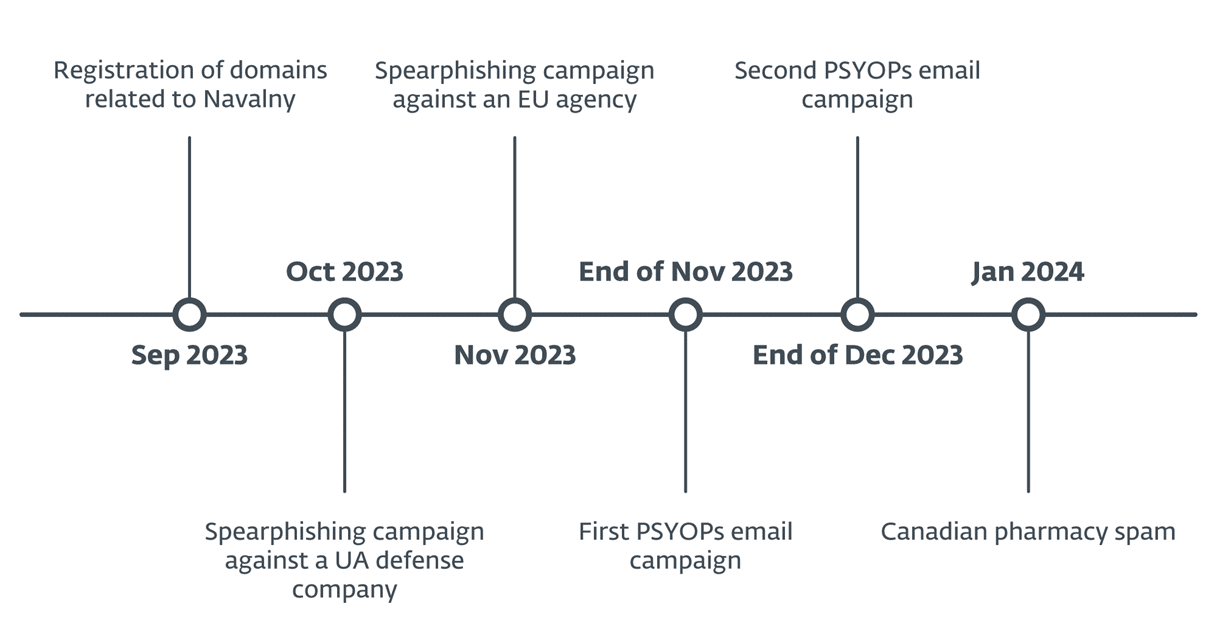
ESET analysts detected a cyber campaign called Operation Texonto. It included a number of disinformation actions (PSYOP – Psychological Operations), conducted via spam email messages. Using such war-themed messages, sent in two waves, Russia-linked groups attempted to influence Ukrainian citizens and lower their morale. The first wave of actions took place in November 2023, and the second at the end of December 2023.
The aim of the first wave of disinformation emails from Texonto was to sow doubt in the minds of Ukrainian residents. For example, one email stated: “This winter, there may be interruptions in heating”. Another, supposedly sent by the Ministry of Health, concerned drug shortages. One of the domains impersonating the Ministry of Agrarian Policy and Food of Ukraine, recommended replacing unavailable medicines with herbs. Another suggestion in this series was to eat dishes made from pigeons, attaching pictures of live and cooked pigeons to the information. It does not seem that there were any malicious links or software in this particular wave of messages. It was based primarily on disinformation, aiming to affect the emotions of recipients, increasing their level of anxiety and demotivating them. False news used motifs typical of Russian propaganda: mainly suggesting to Ukrainian citizens that shortages of medicines, food and heating threaten them during wartime.
The mail server operated by the attackers and used to send emails was reused two weeks later to send typical pharmacy spam in Canada. This category of illegal activities has long been popular in the Russian cybercriminal community. It was also determined that the names of domains, which were part of Operation Texonto, used, among others, the surname of Alexei Navalny, a well-known Russian opposition leader who was in prison and died on 16.02.2024. This means that Operation Texonto most likely included targeted phishing and disinformation actions aimed at Russian dissidents and supporters of the deceased opposition leader.
About a month after the first wave, ESET analysts detected a second PSYOP email campaign, targeted not only at Ukrainians but also at residents of other European countries. Its targets were quite random, with false information being sent to, among others, the Ukrainian government and an Italian footwear manufacturer. According to ESET data, several hundred people received emails as part of this wave. The messages contained, among other things, suggestions of amputating a leg or hand as a solution to avoid being sent to the military. Such messages are characteristic of psychological cyber operations conducted during armed conflicts and are aimed at undermining the morale of specific groups.
In addition, in October 2023, ESET detected a targeted phishing campaign whose aim was a Ukrainian defense industry company, and in November 2023, a campaign aimed at EU agencies, using fabricated Microsoft login pages. The goal of these activities was to steal authentication data for Microsoft Office 365 accounts. According to ESET analysts, due to the similarities in the network infrastructure used in all these activities, it can be assumed that they were related.
– Since the beginning of the aggression against Ukraine, Russia-linked groups, such as Sandworm, have been focusing on disrupting the functioning of Ukrainian IT infrastructure by using malicious data wiping software. Over the past few months, we have observed an increase in cyber espionage activities, especially those carried out by the infamous Gamaredon group. Operation Texonto is another stage in using technology to influence the course of the war – says Matthieu Faou, an ESET researcher who discovered Operation Texonto.
ESET experts underline that the compilation of espionage, disinformation operations, and false news about pharmaceutical topics may remind of the actions of the Callisto group, a well-known cyber espionage group allied with Russia. Some of its members were indicted by the US Department of Justice in December 2023. Callisto attacks government officials, advisory center employees, and military-related organizations through websites designed to mimic popular cloud service providers. The group also conducted disinformation operations, such as an alleged document leak just before the general elections in the UK in 2019. Using their old network infrastructure, they also direct to false pharmaceutical domains.
– Although there are several fundamental similarities between the operations of Texonto and Callisto, we have found no technical point of contact. Currently, therefore, we are not attributing Operation Texonto to any specific cybercriminal group. However, considering the techniques, tactics, procedures (TTP), targeted actions, and disseminated messages, it is highly likely that these activities were conducted by a group allied with Russia – adds Matthieu Faou.
Chronological Course of Operation Texonto: